mirror of
https://github.com/wheelybird/ldap-user-manager.git
synced 2025-01-18 07:32:53 +01:00
Christmas jingles (#55)
* Add account requests, email user on password update, RFC2307BIS autodetection and various bug fixes. * Remove test.php
This commit is contained in:
parent
ff17c6e288
commit
3b8e94ce66
19
Dockerfile
19
Dockerfile
@ -1,8 +1,21 @@
|
||||
FROM php:7.0-apache
|
||||
|
||||
RUN apt-get update && apt-get install -y --no-install-recommends libldb-dev libldap2-dev && rm -rf /var/lib/apt/lists/* && ln -s /usr/lib/x86_64-linux-gnu/libldap.so /usr/lib/libldap.so \
|
||||
&& ln -s /usr/lib/x86_64-linux-gnu/liblber.so /usr/lib/liblber.so
|
||||
RUN docker-php-source extract && docker-php-ext-install -j$(nproc) ldap && docker-php-source delete
|
||||
RUN apt-get update && \
|
||||
apt-get install -y --no-install-recommends \
|
||||
libldb-dev libldap2-dev \
|
||||
libfreetype6-dev \
|
||||
libjpeg-dev \
|
||||
libpng-dev && \
|
||||
rm -rf /var/lib/apt/lists/* && \
|
||||
ln -s /usr/lib/x86_64-linux-gnu/libldap.so /usr/lib/libldap.so && \
|
||||
ln -s /usr/lib/x86_64-linux-gnu/liblber.so /usr/lib/liblber.so
|
||||
|
||||
RUN docker-php-ext-configure gd \
|
||||
--enable-gd-native-ttf \
|
||||
--with-freetype-dir=/usr/include/freetype2 \
|
||||
--with-png-dir=/usr/include \
|
||||
--with-jpeg-dir=/usr/include && \
|
||||
docker-php-ext-install -j$(nproc) ldap gd
|
||||
|
||||
ADD https://github.com/PHPMailer/PHPMailer/archive/v6.2.0.tar.gz /tmp
|
||||
|
||||
|
||||
135
README.md
135
README.md
@ -4,18 +4,17 @@ LDAP User Manager
|
||||
This is a PHP LDAP account manager; a web-based GUI interface which allows you to quickly populate a new LDAP directory and easily manage user accounts and groups. It also has a self-service password change module.
|
||||
It's designed to work with OpenLDAP and to be run as a container. It complements OpenLDAP containers such as [*osixia/openldap*](https://hub.docker.com/r/osixia/openldap/).
|
||||
|
||||
|
||||
|
||||
Features
|
||||
---
|
||||
|
||||
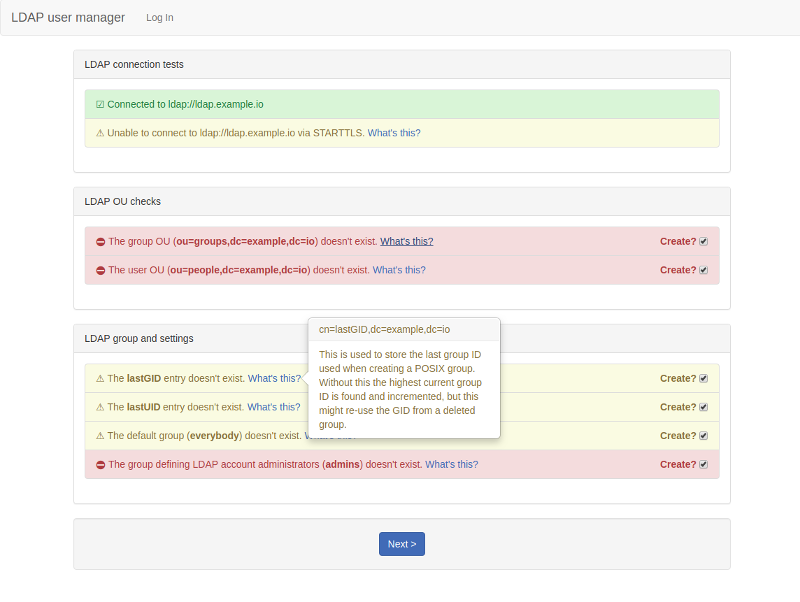
* Setup wizard: this will create the necessary structure to allow you to add users and groups and will set up an initial admin user that can log into the user manager.
|
||||
* Group creation and management.
|
||||
* User account creation and management.
|
||||
* Optionally send an email to the new user with their account credentials.
|
||||
* Optionally send an email to the user with their new or updated account credentials.
|
||||
* Secure password auto-generator: click the button to generate a secure password.
|
||||
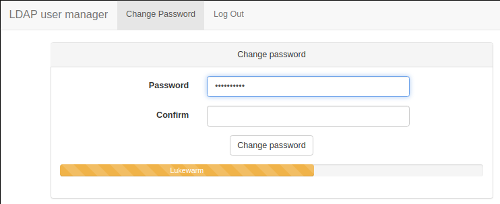
* Password strength indicator.
|
||||
* Self-service password change: non-admin users can log in to change their password.
|
||||
* An optional form for people to request accounts (request emails are sent to an administrator).
|
||||
|
||||
Screenshots
|
||||
---
|
||||
@ -36,26 +35,6 @@ Screenshots
|
||||
|
||||
|
||||
|
||||
A note on your LDAP schema - please read this!
|
||||
---
|
||||
|
||||
By default this application will expect the LDAP server to be using the **RFC2307BIS** schema. OpenLDAP (including the **osixia/openldap** image) uses the older NIS schema as its default schema.
|
||||
|
||||
> :warning: If you haven't explicitly set up the **RFC2307BIS** schema on your LDAP server then you need to set `LDAP_USES_NIS_SCHEMA` to `TRUE` as shown in the Quick start example below.
|
||||
|
||||
**Why should I use RFC2307BIS?**
|
||||
|
||||
The user manager will work with either NIS or BIS, but BIS is recommended as it allows you to use **memberOf** searches. You can enable BIS in **osixia/openldap** by setting `LDAP_RFC2307BIS_SCHEMA` to `true` during the initial setup.
|
||||
|
||||
**Why not make NIS the default?**
|
||||
|
||||
The original versions of this application were set to expect BIS by default. This was before we used specific release versions, so we're expecting the BIS schemas as the default to keep backwards-compatibility for anyone using the `latest` tag.
|
||||
|
||||
**I'm unable to use the BIS schema!**
|
||||
|
||||
If you can't or prefer not to use RFC2307BIS then set `LDAP_USES_NIS_SCHEMA` to `TRUE`. This will create groups solely as the **posixGroup** objectclass, and the default for `LDAP_GROUP_MEMBERSHIP_USES_UID` will `TRUE`.
|
||||
|
||||
|
||||
Quick start
|
||||
---
|
||||
|
||||
@ -72,11 +51,11 @@ docker run \
|
||||
-e "LDAP_ADMINS_GROUP=admins" \
|
||||
-e "LDAP_ADMIN_BIND_DN=cn=admin,dc=example,dc=com" \
|
||||
-e "LDAP_ADMIN_BIND_PWD=secret"\
|
||||
-e "LDAP_USES_NIS_SCHEMA=true" \
|
||||
-e "EMAIL_DOMAIN=ldapusermanager.org"\
|
||||
wheelybird/ldap-user-manager:v1.4
|
||||
-e "LDAP_IGNORE_CERT_ERRORS=true" \
|
||||
-e "EMAIL_DOMAIN=ldapusermanager.org" \
|
||||
wheelybird/ldap-user-manager:v1.5
|
||||
```
|
||||
Change the variable values to suit your environment. You might need to change `LDAP_USES_NIS_SCHEMA` if you're using the BIS schema. Now go to https://lum.example.com/setup.
|
||||
Change the variable values to suit your environment. Now go to https://lum.example.com/setup.
|
||||
|
||||
|
||||
Configuration
|
||||
@ -84,8 +63,8 @@ Configuration
|
||||
|
||||
Configuration is via environmental variables. Please bear the following in mind:
|
||||
|
||||
* This tool needs to bind to LDAP as a user with permissions to modify everything under the base DN.
|
||||
* This interface is designed to work with a fresh LDAP server and should be against populated LDAP directories with caution and at your own risk.
|
||||
* This tool needs to bind to LDAP as a user that has the permissions to modify everything under the base DN.
|
||||
* This interface is designed to work with a fresh LDAP server and should only be against existing, populated LDAP directories with caution and at your own risk.
|
||||
|
||||
Mandatory:
|
||||
----
|
||||
@ -116,17 +95,24 @@ Optional:
|
||||
|
||||
* `LDAP_USER_OU` (default: *people*): The name of the OU used to store user accounts (without the base DN appended).
|
||||
|
||||
* `LDAP_USES_NIS_SCHEMA` (default: *FALSE*): If you use the NIS schema instead of the (preferable) RFC2307BIS schema, set this to `TRUE`. See [A note on your LDAP schema](#a-note-on-your-ldap-schema) for more information.
|
||||
|
||||
* `LDAP_GROUP_OU` (default: *groups*): The name of the OU used to store groups (without the base DN appended).
|
||||
* `LDAP_GROUP_MEMBERSHIP_ATTRIBUTE` (default: *memberUID* or *uniqueMember*): The attribute used when adding a user to a group. If `LDAP_USES_NIS_SCHEMA` is `TRUE` the default is `memberUID`, otherwise it's `uniqueMember`. Explicitly setting this variable will override the default.
|
||||
* `LDAP_GROUP_MEMBERSHIP_USES_UID` (default: *TRUE* or *FALSE*): If *TRUE* then the entry for a member of a group will be just the username. Otherwise it's the member's full DN. If `LDAP_USES_NIS_SCHEMA` is `TRUE` the default is `TRUE`, otherwise it's `FALSE`. Explicitly setting this variable will override the default.
|
||||
|
||||
* `LDAP_REQUIRE_STARTTLS` (default: *TRUE*): If *TRUE* then a TLS connection is required for this interface to work. If set to *FALSE* then the interface will work without STARTTLS, but a warning will be displayed on the page.
|
||||
|
||||
* `LDAP_IGNORE_CERT_ERRORS` (default: *FALSE*): If *TRUE* then problems with the certificate presented by the LDAP server will be ignored (for example FQDN mismatches). Use this if your LDAP server is using a self-signed certificate and you don't have a CA certificate for it or you're connecting to a pool of different servers via round-robin DNS.
|
||||
|
||||
* `LDAP_TLS_CACERT` (no default): If you need to use a specific CA certificate for TLS connections to the LDAP server (when `LDAP_REQUIRE_STARTTLS` is set) then assign the contents of the CA certificate to this variable. e.g. `-e LDAP_TLS_CACERT=$(</path/to/ca.crt)`
|
||||
* `LDAP_TLS_CACERT` (no default): If you need to use a specific CA certificate for TLS connections to the LDAP server (when `LDAP_REQUIRE_STARTTLS` is set) then assign the contents of the CA certificate to this variable. e.g. `-e LDAP_TLS_CACERT="$(</path/to/ca.crt)"` (ensure you're using quotes or you'll get an "invalid reference format: repository name must be lowercase" error.
|
||||
|
||||
**Advanced LDAP settings**
|
||||
|
||||
These settings should only be changed if you're trying to make the user manager work with an LDAP directory that's already populated and the defaults don't work.
|
||||
|
||||
* `LDAP_GROUP_MEMBERSHIP_ATTRIBUTE` (default: *memberUID* or *uniqueMember*): The attribute used when adding a user's account to a group. When the `groupOfMembers` objectClass is detected or force-enabled it defaults to `uniqueMember`, otherwise it'll default to `memberUID`. Explicitly setting this variable will override any default.
|
||||
|
||||
* `LDAP_GROUP_MEMBERSHIP_USES_UID` (default: *TRUE* or *FALSE*): If *TRUE* then the entry for a member of a group will be just the username, otherwise it's the member's full DN. When the `groupOfMembers` objectClass is detected or force-enabled it defaults to `FALSE`, otherwise it'll default to `TRUE`. Explicitly setting this variable will override the default.
|
||||
|
||||
* `FORCE_RFC2307BIS` (default: *FALSE*): Set to *TRUE* if the auto-detection is failing to spot that the RFC2307BIS schema is available. When *FALSE* the user manager will use auto-detection. See [Using the RFC2307BIS schema](#using-the-rfc2307bis-schema) for more information.
|
||||
|
||||
|
||||
**User account settings**
|
||||
|
||||
@ -145,7 +131,9 @@ Optional:
|
||||
* `ACCEPT_WEAK_PASSWORDS` (default: *FALSE*): Set this to *TRUE* to prevent a password being rejected for being too weak. The password strength indicators will still gauge the strength of the password. Don't enable this in a production environment.
|
||||
|
||||
|
||||
**Email settings**
|
||||
**Email sending**
|
||||
|
||||
To send emails you'll need to use an existing SMTP server. Email sending will be disabled if `SMTP_HOSTNAME` isn't set.
|
||||
|
||||
* `SMTP_HOSTNAME` (no default): The hostname of an SMTP server - used to send emails when creating new accounts.
|
||||
|
||||
@ -161,13 +149,18 @@ Optional:
|
||||
|
||||
* `EMAIL_FROM_NAME` (default: *{SITE_NAME}*): The FROM name used when sending out emails. The default name is taken from `SITE_NAME` under **Organisation settings**.
|
||||
|
||||
**Account requests**
|
||||
|
||||
* `ACCOUNT_REQUESTS_ENABLED` (default: *FALSE*): Set to TRUE in order to enable a form that people can fill in to request an account. This will send an email to {ACCOUNT_REQUESTS_EMAIL} with their details and a link to the account creation page where the details will be filled in automatically. You'll need to set up email sending (see **Email sending**, above) for this to work. If this is enabled but email sending isn't then requests will be disabled and an error message sent to the logs.
|
||||
|
||||
* `ACCOUNT_REQUESTS_EMAIL` (default: *{EMAIL_FROM_ADDRESS}*): This is the email address that any requests for a new account are sent to.
|
||||
**Site security settings**
|
||||
|
||||
* `NO_HTTPS` (default: *FALSE*): If you set this to *TRUE* then the server will run in HTTP mode, without any encryption. This is insecure and should only be used for testing.
|
||||
|
||||
* `LOGIN_TIMEOUT_MINS` (default: *10 minutes*): How long before an idle session will be timed out.
|
||||
* `SESSION_TIMEOUT` (default: *10 minutes*): How long before an idle session will be timed out.
|
||||
|
||||
**Debug settings**
|
||||
**Debugging settings**
|
||||
|
||||
* `LDAP_DEBUG` (default: *FALSE*): Set to TRUE to increase the logging level for LDAP requests. This will output passwords to the error log - don't enable this in a production environment. This is for information on problems updating LDAP records and such. To debug problems connecting to the LDAP server in the first place use `LDAP_VERBOSE_CONNECTION_LOGS`.
|
||||
|
||||
@ -177,29 +170,24 @@ Optional:
|
||||
|
||||
* `SMTP_LOG_LEVEL` (default: *0*): Set to between 1-4 to get SMTP logging information (0 disables SMTP debugging logs though it will still display errors). See https://github.com/PHPMailer/PHPMailer/wiki/SMTP-Debugging for details of the levels.
|
||||
|
||||
Webserver SSL setup
|
||||
SSL setup
|
||||
---
|
||||
|
||||
When `NO_HTTPS` is set to **false** (the default), the webserver (Apache HTTPD) expects to find `/opt/ssl/server.key` and `/opt/ssl/server.crt`, and these certificates should match `SERVER_HOSTNAME`. If these files aren't found then the startup script will create self-signed certificates based on `SERVER_HOSTNAME`. To use your own key and certificate then you need to bind-mount a directory containing them to `/opt/ssl`. The script will also look for `/opt/ssl/chain.pem` if you need to add a certificate chain file (the Apache `SSLCertificateChainFile` option).
|
||||
When `NO_HTTPS` is set to **FALSE** (the default), the webserver (Apache HTTPD) expects to find `/opt/ssl/server.key` and `/opt/ssl/server.crt`, and these certificates should match `SERVER_HOSTNAME`. If these files aren't found then the startup script will create self-signed certificates based on `SERVER_HOSTNAME`. To use your own key and certificate then you need to bind-mount a directory containing them to `/opt/ssl`. You can also add a certificate chain file (the Apache `SSLCertificateChainFile` option) if needed - name it `chain.pem` and place it in the same directory as `server.key` and `server.crt` .
|
||||
|
||||
e.g.:
|
||||
For example, if your key and certificate files are in `/home/myaccount/ssl` you can bind-mount that folder by adding this line to the docker run example above, just after the last line starting with `-e`:
|
||||
```
|
||||
docker run \
|
||||
--detach \
|
||||
--name=lum \
|
||||
-p 80:80 \
|
||||
-p 443:443 \
|
||||
-e SERVER_HOSTNAME=lum.ldapusermanager.org \
|
||||
-v /your/ssl/cert/dir:/opt/ssl \
|
||||
...
|
||||
...
|
||||
-v /home/myaccount/ssl:/opt/ssl \
|
||||
|
||||
```
|
||||
|
||||
Initial setup
|
||||
---
|
||||
|
||||
Ideally you'll be using this against an empty LDAP directory. You can use the setup utility to create the LDAP structures that this tool needs in order to create accounts and groups. Go to `https://_website-hostname_/setup` to get started. You need to log in with the password for the admin user as set by `LDAP_ADMIN_BIND_DN`.
|
||||
Ideally you'll be using this against an empty LDAP directory. You can use the setup utility to create the LDAP structures that this user manager needs in order to create accounts and groups. Go to `https://{SERVER_HOSTNAME}/setup` to get started (replace `{SERVER_HOSTNAME}` with whatever you set `SERVER_HOSTNAME` to in the Docker run command).
|
||||
|
||||
The log in password is the admin user's password (what `LDAP_ADMIN_BIND_DN` was set to).
|
||||
|
||||
The setup utility will create the user and account trees, records that store the last UID and GID used when creating a user account or group, a group for admins and the initial admin account.
|
||||
|
||||
|
||||
@ -210,7 +198,7 @@ Sending emails
|
||||
|
||||
When you create an account you'll have an option to send an email to the person you created the account for. The email will give them their new username, password and a link to the self-service password change utility.
|
||||
|
||||
Emails are sent via SMTP, so you'll need to be able to connect to an SMTP server and pass in the settings for that server via environmental variables - see **Email settings** above.
|
||||
Emails are sent via SMTP, so you'll need to be able to connect to an SMTP server and pass in the settings for that server via environmental variables - see **Email sending** above.
|
||||
If you haven't passed in those settings or if the account you've created has no (valid) email address then the option to send an email will be disabled.
|
||||
|
||||
When the account is created you'll be told if the email was sent or not but be aware that just because your SMTP server accepted the email it doesn't mean that it was able to deliver it. If you get a message saying the email wasn't sent then check the logs for the error. You can increase the log level (`SMTP_LOG_LEVEL`) to above 0 in order to see SMTP debug logs.
|
||||
@ -232,21 +220,35 @@ Anything else in the `USERNAME_FORMAT` string is left as defined, but the userna
|
||||
If `EMAIL_DOMAIN` is set then the email address field will be automatically updated in the form of `username@email_domain`. Entering anything manually in that field will stop the automatic update of the email field.
|
||||
|
||||
|
||||
Using the RFC2307BIS schema
|
||||
---
|
||||
|
||||
The user manager will attempt detect if your LDAP server has the RFC2307BIS schema available and, if it does, use it when creating groups. This will allow you to use `memberOf` in LDAP searches which gives you an easy way to check if a user is a member of a group. For example: `(&(objectClass=posixAccount)(memberof=cn=somegroup,ou=groups,dc=ldapusermanager,dc=org))`. See (this guide)[https://unofficialaciguide.com/2019/07/31/ldap-schemas-for-aci-administrators-rfc2307-vs-rfc2307bis/] for more information.
|
||||
|
||||
With OpenLDAP this schema isn't normally available by default; you need to configure your server to use the **RFC2307BIS** schema when setting up your directory.
|
||||
|
||||
If for some reason you do have the schema available but it isn't being detected then you can force it's use by setting `FORCE_ENABLE_GROUP_OF_MEMBERS` to `TRUE`.
|
||||
**Note**: if you force-enable using RFC2307BIS but your LDAP server doesn't have that schema available then creating and adding users to groups won't work and the user manager will throw errors.
|
||||
|
||||
If you plan on using [osixia/openldap](https://github.com/osixia/docker-openldap) as your LDAP server you can enable the RFC2307BIS schema by setting `LDAP_RFC2307BIS_SCHEMA` to `true` during the initial setup.
|
||||
|
||||
|
||||
|
||||
Testing with an LDAP container
|
||||
--
|
||||
|
||||
This will set up an OpenLDAP container you can use to test the user manager against. It uses the BIS schema. This won't be using HTTPS or TLS, so don't use this in production.
|
||||
This will set up an OpenLDAP container you can use to test the user manager against. It uses the RFC2307BIS schema.
|
||||
```
|
||||
docker run \
|
||||
--detach \
|
||||
--restart unless-stopped \
|
||||
--name openldap \
|
||||
-e LDAP_ORGANISATION=wheelybird \
|
||||
-e LDAP_DOMAIN=wheelybird.com \
|
||||
-e LDAP_ADMIN_PASSWORD=change_me \
|
||||
-e LDAP_RFC2307BIS_SCHEMA=true \
|
||||
-e LDAP_REMOVE_CONFIG_AFTER_SETUP=true \
|
||||
-e LDAP_TLS=false \
|
||||
-e "LDAP_ORGANISATION=ldapusermanager" \
|
||||
-e "LDAP_DOMAIN=ldapusermanager.org" \
|
||||
-e "LDAP_ADMIN_PASSWORD=change_me" \
|
||||
-e "LDAP_RFC2307BIS_SCHEMA=true" \
|
||||
-e "LDAP_REMOVE_CONFIG_AFTER_SETUP=true" \
|
||||
-e "LDAP_TLS_VERIFY_CLIENT=never" \
|
||||
-p 389:389
|
||||
--volume /opt/docker/openldap/var_lib_ldap:/var/lib/ldap \
|
||||
--volume /opt/docker/openldap/etc_ldap_slapd.d:/etc/ldap/slapd.d \
|
||||
@ -256,13 +258,14 @@ docker run \
|
||||
--detach \
|
||||
--name=lum \
|
||||
-p 80:80 \
|
||||
-e SERVER_HOSTNAME=localhost \
|
||||
-e LDAP_URI=ldap://172.17.0.1 \
|
||||
-e LDAP_BASE_DN=dc=wheelybird,dc=com \
|
||||
-e LDAP_ADMINS_GROUP=admins \
|
||||
-e LDAP_ADMIN_BIND_DN="cn=admin,dc=wheelybird,dc=com" \
|
||||
-e LDAP_ADMIN_BIND_PWD=change_me \
|
||||
-e NO_HTTPS=TRUE \
|
||||
-p 443:443 \
|
||||
-e "SERVER_HOSTNAME=localhost" \
|
||||
-e "LDAP_URI=ldap://172.17.0.1" \
|
||||
-e "LDAP_BASE_DN=dc=ldapusermanager,dc=org" \
|
||||
-e "LDAP_ADMINS_GROUP=admins" \
|
||||
-e "LDAP_ADMIN_BIND_DN=cn=admin,dc=ldapusermanager,dc=org" \
|
||||
-e "LDAP_ADMIN_BIND_PWD=change_me" \
|
||||
-e "LDAP_IGNORE_CERT_ERRORS=true" \
|
||||
wheelybird/ldap-user-manager:latest
|
||||
```
|
||||
Now go to http://localhost/setup - the password is `change_me` (unless you changed it).
|
||||
Now go to https://localhost/setup - the password is `change_me` (unless you changed it). As this will use self-signed certificates you might need to tell your browser to ignore certificate warnings.
|
||||
|
||||
@ -103,7 +103,7 @@ EoCertConf
|
||||
########################
|
||||
#Create Apache config
|
||||
|
||||
if [ -f "/opt/tls/chain.pem" ]; then ssl_chain="SSLCertificateChainFile /opt/tls/chain.pem"; fi
|
||||
if [ -f "${ssl_dir}/chain.pem" ]; then ssl_chain="SSLCertificateChainFile ${ssl_dir}/chain.pem"; fi
|
||||
|
||||
cat <<EoHTTPSC >/etc/apache2/sites-enabled/lum.conf
|
||||
|
||||
|
||||
@ -48,9 +48,8 @@ if (isset($_POST['delete_user'])) {
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
#'
|
||||
$people = ldap_get_user_list($ldap_connection);
|
||||
ldap_close($ldap_connection);
|
||||
|
||||
?>
|
||||
<div class="container">
|
||||
@ -64,15 +63,20 @@ ldap_close($ldap_connection);
|
||||
<th>First name</th>
|
||||
<th>Last name</th>
|
||||
<th>Email</th>
|
||||
<th>Member of</th>
|
||||
</tr>
|
||||
</thead>
|
||||
<tbody>
|
||||
<?php
|
||||
foreach ($people as $username => $attribs){
|
||||
|
||||
$group_membership = ldap_user_group_membership($ldap_connection,$username);
|
||||
|
||||
print " <tr>\n <td><a href='/$THIS_MODULE_PATH/show_user.php?username=" . urlencode($username) . "'>$username</a></td>\n";
|
||||
print " <td>" . $people[$username]['givenname'] . "</td>\n";
|
||||
print " <td>" . $people[$username]['sn'] . "</td>\n";
|
||||
print " <td>" . $people[$username]['mail'] . "</td>\n";
|
||||
print " <td>" . implode(", ", $group_membership) . "</td>\n";
|
||||
print " </tr>\n";
|
||||
}
|
||||
?>
|
||||
@ -81,5 +85,6 @@ foreach ($people as $username => $attribs){
|
||||
</div>
|
||||
<?php
|
||||
|
||||
ldap_close($ldap_connection);
|
||||
render_footer();
|
||||
?>
|
||||
|
||||
@ -33,9 +33,26 @@ $mismatched_passwords = FALSE;
|
||||
$invalid_username = FALSE;
|
||||
$weak_password = FALSE;
|
||||
$invalid_email = FALSE;
|
||||
$disabled_email_tickbox = TRUE;
|
||||
|
||||
if ($SMTP['host'] != "") { $can_send_email = TRUE; } else { $can_send_email = FALSE; }
|
||||
if (isset($_GET['account_request'])) {
|
||||
|
||||
$first_name=filter_var($_GET['first_name'], FILTER_SANITIZE_STRING);
|
||||
$last_name=filter_var($_GET['last_name'], FILTER_SANITIZE_STRING);
|
||||
$email=filter_var($_GET['email'], FILTER_SANITIZE_EMAIL);
|
||||
$username = generate_username($first_name,$last_name);
|
||||
|
||||
if ($email == "") {
|
||||
if (isset($EMAIL_DOMAIN)) {
|
||||
$email = $username . "@" . $EMAIL_DOMAIN;
|
||||
$disabled_email_tickbox = FALSE;
|
||||
}
|
||||
}
|
||||
else {
|
||||
$disabled_email_tickbox = FALSE;
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
if (isset($_POST['create_account'])) {
|
||||
|
||||
@ -53,7 +70,7 @@ if (isset($_POST['create_account'])) {
|
||||
if (preg_match("/\"|'/",$password)) { $invalid_password = TRUE; }
|
||||
if ($_POST['password'] != $_POST['password_match']) { $mismatched_passwords = TRUE; }
|
||||
if (!preg_match("/$USERNAME_REGEX/",$username)) { $invalid_username = TRUE; }
|
||||
if (isset($_POST['send_email']) and isset($email) and $can_send_email == TRUE) { $send_user_email = TRUE; }
|
||||
if (isset($_POST['send_email']) and isset($email) and $EMAIL_SENDING_ENABLED == TRUE) { $send_user_email = TRUE; }
|
||||
|
||||
|
||||
if ( isset($first_name)
|
||||
@ -84,8 +101,7 @@ You've been set up with an account for $ORGANISATION_NAME. Your credentials are
|
||||
Username: $username
|
||||
Password: $password
|
||||
|
||||
You should change your password as soon as possible. Log into the account manager at ${SITE_PROTOCOL}${SERVER_HOSTNAME}/log_in using your credentials.
|
||||
Once logged in you can change your password at ${SITE_PROTOCOL}${SERVER_HOSTNAME}/change_password/
|
||||
You should change your password as soon as possible. Go to ${SITE_PROTOCOL}${SERVER_HOSTNAME}/change_password and log in using your new credentials. This will take you to a page where you can change your password.
|
||||
EoT;
|
||||
|
||||
include_once "mail_functions.inc.php";
|
||||
@ -216,15 +232,15 @@ render_js_email_generator('username','email');
|
||||
|
||||
function check_email_validity(email) {
|
||||
|
||||
var check_regex = /^(([^<>()[\]\\.,;:\s@\"]+(\.[^<>()[\]\\.,;:\s@\"]+)*)|(\".+\"))@((\[[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\])|(([a-zA-Z\-0-9]+\.)+[a-zA-Z]{2,}))$/;
|
||||
var check_regex = <?php print $JS_EMAIL_REGEX; ?>
|
||||
|
||||
if (! check_regex.test(email) ) {
|
||||
document.getElementById("email_div").classList.add("has-error");
|
||||
<?php if ($can_send_email == TRUE) { ?>document.getElementById("send_email_checkbox").disabled = true;<?php } ?>
|
||||
<?php if ($EMAIL_SENDING_ENABLED == TRUE) { ?>document.getElementById("send_email_checkbox").disabled = true;<?php } ?>
|
||||
}
|
||||
else {
|
||||
document.getElementById("email_div").classList.remove("has-error");
|
||||
<?php if ($can_send_email == TRUE) { ?>document.getElementById("send_email_checkbox").disabled = false;<?php } ?>
|
||||
<?php if ($EMAIL_SENDING_ENABLED == TRUE) { ?>document.getElementById("send_email_checkbox").disabled = false;<?php } ?>
|
||||
}
|
||||
|
||||
}
|
||||
@ -289,11 +305,11 @@ render_js_email_generator('username','email');
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<?php if ($can_send_email == TRUE and $admin_setup != TRUE) { ?>
|
||||
<?php if ($EMAIL_SENDING_ENABLED == TRUE and $admin_setup != TRUE) { ?>
|
||||
<div class="form-group" id="send_email_div">
|
||||
<label for="send_email" class="col-sm-3 control-label"> </label>
|
||||
<div class="col-sm-6">
|
||||
<input tabindex="8" type="checkbox" class="form-check-input" id="send_email_checkbox" name="send_email" disabled> Email these credentials to the user?
|
||||
<input tabindex="8" type="checkbox" class="form-check-input" id="send_email_checkbox" name="send_email" <?php if ($disabled_email_tickbox == TRUE) { print "disabled"; } ?>> Email these credentials to the user?
|
||||
</div>
|
||||
</div>
|
||||
<?php } ?>
|
||||
|
||||
@ -15,6 +15,8 @@ $mismatched_passwords = FALSE;
|
||||
$invalid_username = FALSE;
|
||||
$weak_password = FALSE;
|
||||
|
||||
if ($SMTP['host'] != "") { $can_send_email = TRUE; } else { $can_send_email = FALSE; }
|
||||
|
||||
$attribute_map = array( "givenname" => "First name",
|
||||
"sn" => "Last name",
|
||||
"uidnumber" => "UID",
|
||||
@ -95,9 +97,38 @@ if ($ldap_search) {
|
||||
}
|
||||
}
|
||||
|
||||
if (isset($_POST['send_email']) and isset($user[0]['mail'][0]) and $can_send_email == TRUE) {
|
||||
$user_email = $user[0]['mail'][0];
|
||||
$first_name = $user[0]['givenname'][0];
|
||||
$last_name = $user[0]['sn'][0];
|
||||
}
|
||||
|
||||
$updated_account = ldap_mod_replace($ldap_connection, $user[0]['dn'] , $to_update);
|
||||
|
||||
$sent_email_message="";
|
||||
if ($updated_account and isset($user_email)) {
|
||||
|
||||
$mail_subject = "Your $ORGANISATION_NAME password has been reset.";
|
||||
|
||||
$mail_body = <<<EoT
|
||||
Your password for $ORGANISATION_NAME has been reset. Your new credentials are:
|
||||
|
||||
Username: $username
|
||||
Password: $password
|
||||
|
||||
You should change your password as soon as possible. Go to ${SITE_PROTOCOL}${SERVER_HOSTNAME}/change_password and log in using your new credentials. This will take you to a page where you can change your password.
|
||||
EoT;
|
||||
|
||||
include_once "mail_functions.inc.php";
|
||||
$sent_email = send_email($user_email,"$first_name $last_name",$mail_subject,$mail_body);
|
||||
if ($sent_email) {
|
||||
$sent_email_message .= " An email sent to $user_email.";
|
||||
}
|
||||
else {
|
||||
$sent_email_message .= " Unfortunately the email wasn't sent; check the logs for more information.";
|
||||
}
|
||||
}
|
||||
|
||||
if ($updated_account) {
|
||||
?>
|
||||
<script>
|
||||
@ -107,7 +138,7 @@ if ($ldap_search) {
|
||||
</script>
|
||||
<div class="alert alert-success" role="alert">
|
||||
<button type="button" class="close" data-dismiss="alert" aria-label="Close"><span aria-hidden="TRUE">×</span></button>
|
||||
<strong>Success!</strong> The group has been updated.
|
||||
<strong>Success!</strong> The account has been updated.<?php print $sent_email_message; ?>
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
@ -118,9 +149,9 @@ if ($ldap_search) {
|
||||
$(".alert").fadeTo(500, 0).slideUp(500, function(){ $(this).remove(); });
|
||||
}, 4000);
|
||||
</script>
|
||||
<div class="alert alert-success" role="alert">
|
||||
<div class="alert alert-danger" role="alert">
|
||||
<button type="button" class="close" data-dismiss="alert" aria-label="Close"><span aria-hidden="TRUE">×</span></button>
|
||||
<strong>Success!</strong> The group has been updated.
|
||||
<strong>Error!</strong> There was a problem updating the account. Check the logs for more information.
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
@ -151,13 +182,7 @@ if ($ldap_search) {
|
||||
|
||||
$all_groups = ldap_get_group_list($ldap_connection);
|
||||
|
||||
$currently_member_of = array();
|
||||
|
||||
foreach ($all_groups as $this_group) {
|
||||
if (ldap_is_group_member($ldap_connection,$this_group,$username)) {
|
||||
array_push($currently_member_of,$this_group);
|
||||
}
|
||||
}
|
||||
$currently_member_of = ldap_user_group_membership($ldap_connection,$username);
|
||||
|
||||
$not_member_of = array_diff($all_groups,$currently_member_of);
|
||||
|
||||
@ -177,7 +202,6 @@ if ($ldap_search) {
|
||||
$groups_to_add = array_diff($updated_group_membership,$currently_member_of);
|
||||
$groups_to_del = array_diff($currently_member_of,$updated_group_membership);
|
||||
|
||||
|
||||
foreach ($groups_to_del as $this_group) {
|
||||
ldap_delete_member_from_group($ldap_connection,$this_group,$username);
|
||||
}
|
||||
@ -196,7 +220,7 @@ if ($ldap_search) {
|
||||
</script>
|
||||
<div class="alert alert-success" role="alert">
|
||||
<button type="button" class="close" data-dismiss="alert" aria-label="Close"><span aria-hidden="TRUE">×</span></button>
|
||||
<strong>Success!</strong> The group has been updated.
|
||||
<strong>Success!</strong> The group membership has been updated.
|
||||
</div>
|
||||
|
||||
<?php
|
||||
@ -323,6 +347,34 @@ $full_dn = $user[0]['dn'];
|
||||
|
||||
|
||||
</script>
|
||||
|
||||
<script>
|
||||
|
||||
function check_if_we_should_enable_sending_email() {
|
||||
|
||||
var check_regex = <?php print $JS_EMAIL_REGEX; ?>
|
||||
|
||||
|
||||
<?php if ($can_send_email == TRUE) { ?>
|
||||
if (check_regex.test(document.getElementById("mail").value) && document.getElementById("password").value.length > 0 ) {
|
||||
document.getElementById("send_email_checkbox").disabled = false;
|
||||
}
|
||||
else {
|
||||
document.getElementById("send_email_checkbox").disabled = true;
|
||||
}
|
||||
|
||||
<?php } ?>
|
||||
if (check_regex.test(document.getElementById('mail').value)) {
|
||||
document.getElementById("mail_div").classList.remove("has-error");
|
||||
}
|
||||
else {
|
||||
document.getElementById("mail_div").classList.add("has-error");
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
</script>
|
||||
|
||||
<div class="container">
|
||||
<div class="col-sm-7">
|
||||
|
||||
@ -347,10 +399,12 @@ $full_dn = $user[0]['dn'];
|
||||
|
||||
foreach ($attribute_map as $key => $value) {
|
||||
?>
|
||||
<div class="form-group">
|
||||
<div class="form-group" id="<?php print $key; ?>_div">
|
||||
<label for="<?php print $key; ?>" class="col-sm-3 control-label"><?php print $value; ?></label>
|
||||
<div class="col-sm-6">
|
||||
<input type="text" class="form-control" id="<?php print $key; ?>" name="<?php print $key; ?>" value="<?php print $user[0][$key][0]; ?>">
|
||||
<input type="text" class="form-control" id="<?php print $key; ?>" name="<?php print $key; ?>" value="<?php print $user[0][$key][0]; ?>" <?php
|
||||
if ($key == "mail") { print 'onkeyup="check_if_we_should_enable_sending_email();"'; }
|
||||
?>>
|
||||
</div>
|
||||
</div>
|
||||
<?php
|
||||
@ -360,10 +414,10 @@ $full_dn = $user[0]['dn'];
|
||||
<div class="form-group" id="password_div">
|
||||
<label for="password" class="col-sm-3 control-label">Password</label>
|
||||
<div class="col-sm-6">
|
||||
<input type="password" class="form-control" id="password" name="password" onkeyup="back_to_hidden('password','confirm');">
|
||||
<input type="password" class="form-control" id="password" name="password" onkeyup="back_to_hidden('password','confirm'); check_if_we_should_enable_sending_email();">
|
||||
</div>
|
||||
<div class="col-sm-1">
|
||||
<input type="button" class="btn btn-sm" id="password_generator" onclick="random_password();" value="Generate password">
|
||||
<input type="button" class="btn btn-sm" id="password_generator" onclick="random_password(); check_if_we_should_enable_sending_email();" value="Generate password">
|
||||
</div>
|
||||
</div>
|
||||
|
||||
@ -374,6 +428,16 @@ $full_dn = $user[0]['dn'];
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<?php if ($can_send_email == TRUE) { ?>
|
||||
<div class="form-group" id="send_email_div">
|
||||
<label for="send_email" class="col-sm-3 control-label"> </label>
|
||||
<div class="col-sm-6">
|
||||
<input type="checkbox" class="form-check-input" id="send_email_checkbox" name="send_email" disabled> Email the updated credentials to the user?
|
||||
</div>
|
||||
</div>
|
||||
<?php } ?>
|
||||
|
||||
|
||||
<div class="form-group">
|
||||
<p align='center'><button type="submit" class="btn btn-default">Update account details</button></p>
|
||||
</div>
|
||||
|
||||
26
www/account_manager/test.php
Normal file
26
www/account_manager/test.php
Normal file
@ -0,0 +1,26 @@
|
||||
<?php
|
||||
|
||||
set_include_path( ".:" . __DIR__ . "/../includes/");
|
||||
|
||||
include_once "web_functions.inc.php";
|
||||
include_once "ldap_functions.inc.php";
|
||||
include_once "module_functions.inc.php";
|
||||
|
||||
|
||||
render_header("LDAP manager");
|
||||
render_submenu();
|
||||
|
||||
$ldap_connection = open_ldap_connection();
|
||||
|
||||
|
||||
print "<pre>";
|
||||
print $schema_base_dn . "\n";
|
||||
print_r($gom_results);
|
||||
print "\n\n\n\n";
|
||||
print_r($gom_r_search);
|
||||
print "</pre>";
|
||||
|
||||
|
||||
|
||||
render_footer();
|
||||
?>
|
||||
@ -1,5 +1,7 @@
|
||||
<?php
|
||||
|
||||
$log_prefix = "";
|
||||
|
||||
#Mandatory
|
||||
|
||||
$LDAP['uri'] = getenv('LDAP_URI');
|
||||
@ -14,23 +16,15 @@
|
||||
$LDAP['group_ou'] = (getenv('LDAP_GROUP_OU') ? getenv('LDAP_GROUP_OU') : 'groups');
|
||||
$LDAP['user_ou'] = (getenv('LDAP_USER_OU') ? getenv('LDAP_USER_OU') : 'people');
|
||||
|
||||
$LDAP['nis_schema'] = ((strcasecmp(getenv('LDAP_USES_NIS_SCHEMA'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
$LDAP['forced_rfc2308bis'] = ((strcasecmp(getenv('FORCE_RFC2307BIS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
|
||||
if ($LDAP['nis_schema'] == TRUE) {
|
||||
$default_membership_attribute = 'memberuid';
|
||||
$default_group_membership_uses_uid = TRUE;
|
||||
}
|
||||
else {
|
||||
$default_membership_attribute = 'uniquemember';
|
||||
$default_group_membership_uses_uid = FALSE;
|
||||
}
|
||||
|
||||
$LDAP['group_membership_attribute'] = (getenv('LDAP_GROUP_MEMBERSHIP_ATTRIBUTE') ? getenv('LDAP_GROUP_MEMBERSHIP_ATTRIBUTE') : $default_membership_attribute);
|
||||
$LDAP['group_membership_uses_uid'] = ((strcasecmp(getenv('LDAP_GROUP_MEMBERSHIP_USES_UID'),'TRUE') == 0) ? TRUE : $default_group_membership_uses_uid);
|
||||
if (getenv('LDAP_GROUP_MEMBERSHIP_ATTRIBUTE')) { $LDAP['group_membership_attribute'] = getenv('LDAP_GROUP_MEMBERSHIP_ATTRIBUTE'); }
|
||||
if (getenv('LDAP_GROUP_MEMBERSHIP_USES_UID') and strtoupper(getenv('LDAP_GROUP_MEMBERSHIP_USES_UID')) == TRUE ) { $LDAP['group_membership_uses_uid'] = TRUE; }
|
||||
|
||||
$LDAP['account_attribute'] = 'uid';
|
||||
$LDAP['require_starttls'] = ((strcasecmp(getenv('LDAP_REQUIRE_STARTTLS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
$LDAP['ignore_cert_errors'] = ((strcasecmp(getenv('LDAP_IGNORE_CERT_ERRORS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
$LDAP['rfc2307bis_check_run'] = FALSE;
|
||||
|
||||
$DEFAULT_USER_GROUP = (getenv('DEFAULT_USER_GROUP') ? getenv('DEFAULT_USER_GROUP') : 'everybody');
|
||||
$DEFAULT_USER_SHELL = (getenv('DEFAULT_USER_SHELL') ? getenv('DEFAULT_USER_SHELL') : '/bin/bash');
|
||||
@ -46,7 +40,7 @@
|
||||
if (getenv('PASSWORD_HASH')) { $PASSWORD_HASH = strtoupper(getenv('PASSWORD_HASH')); }
|
||||
|
||||
$ACCEPT_WEAK_PASSWORDS = ((strcasecmp(getenv('ACCEPT_WEAK_PASSWORDS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
$LOGIN_TIMEOUT_MINS = (getenv('SESSION_TIMEOUT') ? getenv('SESSION_TIMEOUT') : 10);
|
||||
$SESSION_TIMEOUT = (getenv('SESSION_TIMEOUT') ? getenv('SESSION_TIMEOUT') : 10);
|
||||
|
||||
$LDAP_DEBUG = ((strcasecmp(getenv('LDAP_DEBUG'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
$LDAP_VERBOSE_CONNECTION_LOGS = ((strcasecmp(getenv('LDAP_VERBOSE_CONNECTION_LOGS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
@ -76,11 +70,22 @@
|
||||
$EMAIL['from_address'] = (getenv('EMAIL_FROM_ADDRESS') ? getenv('EMAIL_FROM_ADDRESS') : "admin@" . $default_email_from_domain );
|
||||
$EMAIL['from_name'] = (getenv('EMAIL_FROM_NAME') ? getenv('EMAIL_FROM_NAME') : $SITE_NAME );
|
||||
|
||||
$NO_HTTPS = ((strcasecmp(getenv('NO_HTTPS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
if ($SMTP['host'] != "") { $EMAIL_SENDING_ENABLED = TRUE; } else { $EMAIL_SENDING_ENABLED = FALSE; }
|
||||
|
||||
|
||||
###
|
||||
|
||||
$log_prefix = "";
|
||||
$ACCOUNT_REQUESTS_ENABLED = ((strcasecmp(getenv('ACCOUNT_REQUESTS_ENABLED'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
if ($EMAIL_SENDING_ENABLED == FALSE) {
|
||||
$ACCOUNT_REQUESTS_ENABLED = FALSE;
|
||||
error_log("$log_prefix Config: ACCOUNT_REQUESTS_ENABLED was set to TRUE but SMTP_HOSTNAME wasn't set, so account requesting has been disabled as we can't send out the request email",0);
|
||||
}
|
||||
|
||||
$ACCOUNT_REQUESTS_EMAIL = (getenv('ACCOUNT_REQUESTS_EMAIL') ? getenv('ACCOUNT_REQUESTS_EMAIL') : $EMAIL['from_address']);
|
||||
|
||||
###
|
||||
|
||||
$NO_HTTPS = ((strcasecmp(getenv('NO_HTTPS'),'TRUE') == 0) ? TRUE : FALSE);
|
||||
|
||||
###
|
||||
|
||||
|
||||
@ -6,7 +6,7 @@ $LDAP_IS_SECURE = FALSE;
|
||||
|
||||
function open_ldap_connection() {
|
||||
|
||||
global $log_prefix, $LDAP, $SENT_HEADERS, $LDAP_DEBUG, $LDAP_IS_SECURE;
|
||||
global $log_prefix, $LDAP, $SENT_HEADERS, $LDAP_DEBUG, $LDAP_IS_SECURE, $LDAP_VERBOSE_CONNECTION_LOGS;
|
||||
|
||||
if ($LDAP['ignore_cert_errors'] == TRUE) { putenv('LDAPTLS_REQCERT=never'); }
|
||||
$ldap_connection = @ ldap_connect($LDAP['uri']);
|
||||
@ -423,6 +423,8 @@ function ldap_get_group_members($ldap_connection,$group_name,$start=0,$entries=N
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
$ldap_search_query = "(cn=". ldap_escape($group_name, "", LDAP_ESCAPE_FILTER) . ")";
|
||||
$ldap_search = @ ldap_search($ldap_connection, "${LDAP['group_dn']}", $ldap_search_query, array($LDAP['group_membership_attribute']));
|
||||
|
||||
@ -468,6 +470,8 @@ function ldap_is_group_member($ldap_connection,$group_name,$username) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
$ldap_search_query = "(cn=" . ldap_escape($group_name, "", LDAP_ESCAPE_FILTER) . ")";
|
||||
$ldap_search = ldap_search($ldap_connection, "${LDAP['group_dn']}", $ldap_search_query);
|
||||
$result = ldap_get_entries($ldap_connection, $ldap_search);
|
||||
@ -486,12 +490,42 @@ function ldap_is_group_member($ldap_connection,$group_name,$username) {
|
||||
}
|
||||
|
||||
|
||||
##################################
|
||||
|
||||
function ldap_user_group_membership($ldap_connection,$username) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
if ($LDAP['group_membership_uses_uid'] == FALSE) {
|
||||
$username = "${LDAP['account_attribute']}=$username,${LDAP['user_dn']}";
|
||||
}
|
||||
|
||||
$ldap_search_query = "(&(objectClass=posixGroup)(${LDAP['group_membership_attribute']}=${username}))";
|
||||
$ldap_search = ldap_search($ldap_connection, "${LDAP['group_dn']}", $ldap_search_query, array('cn'));
|
||||
$result = ldap_get_entries($ldap_connection, $ldap_search);
|
||||
|
||||
$groups = array();
|
||||
foreach ($result as $record) {
|
||||
if (isset($record['cn'][0])) {
|
||||
array_push($groups, $record['cn'][0]);
|
||||
}
|
||||
}
|
||||
sort($groups);
|
||||
return $groups;
|
||||
|
||||
}
|
||||
|
||||
|
||||
##################################
|
||||
|
||||
function ldap_new_group($ldap_connection,$group_name) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
if (isset($group_name)) {
|
||||
|
||||
$ldap_search_query = "(cn=" . ldap_escape($group_name, "", LDAP_ESCAPE_FILTER) . ",${LDAP['group_dn']})";
|
||||
@ -503,7 +537,7 @@ function ldap_new_group($ldap_connection,$group_name) {
|
||||
$highest_gid = ldap_get_highest_id($ldap_connection,'gid');
|
||||
$new_gid = $highest_gid + 1;
|
||||
|
||||
if ($LDAP['nis_schema'] == TRUE) {
|
||||
if ($rfc2307bis_available == FALSE) {
|
||||
$new_group_array=array( 'objectClass' => array('top','posixGroup'),
|
||||
'cn' => $group_name,
|
||||
'gidNumber' => $new_gid
|
||||
@ -714,6 +748,8 @@ function ldap_add_member_to_group($ldap_connection,$group_name,$username) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
$group_dn = "cn=" . ldap_escape($group_name, "", LDAP_ESCAPE_FILTER) . ",${LDAP['group_dn']}";
|
||||
|
||||
if ($LDAP['group_membership_uses_uid'] == FALSE) {
|
||||
@ -741,6 +777,8 @@ function ldap_delete_member_from_group($ldap_connection,$group_name,$username) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
if ($LDAP['rfc2307bis_check_run'] != TRUE) { $rfc2307bis_available = ldap_detect_rfc2307bis($ldap_connection); }
|
||||
|
||||
$group_dn = "cn=" . ldap_escape($group_name, "", LDAP_ESCAPE_FILTER) . ",${LDAP['group_dn']}";
|
||||
|
||||
if ($LDAP['group_membership_uses_uid'] == FALSE) {
|
||||
@ -802,4 +840,76 @@ function ldap_change_password($ldap_connection,$username,$new_password) {
|
||||
}
|
||||
|
||||
|
||||
##################################
|
||||
|
||||
function ldap_detect_rfc2307bis($ldap_connection) {
|
||||
|
||||
global $log_prefix, $LDAP, $LDAP_DEBUG;
|
||||
|
||||
$bis_available = FALSE;
|
||||
|
||||
if ($LDAP['forced_rfc2307bis'] == TRUE) {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - skipping autodetection because FORCE_RFC2307BIS is TRUE"); }
|
||||
$bis_available = TRUE;
|
||||
}
|
||||
else {
|
||||
|
||||
$schema_base_query = @ ldap_read($ldap_connection,"","subschemaSubentry=*",array('subschemaSubentry'));
|
||||
|
||||
if (!$schema_base_query) {
|
||||
error_log("$log_prefix LDAP RFC2307BIS detection - unable to query LDAP for objectClasses under ${schema_base_dn}:" . ldap_error($ldap_connection));
|
||||
error_log("$log_prefix LDAP RFC2307BIS detection - we'll assume that the RFC2307BIS schema isn't available. Set FORCE_RFC2307BIS to TRUE if you DO use RFC2307BIS.");
|
||||
}
|
||||
else {
|
||||
$schema_base_results = @ ldap_get_entries($ldap_connection, $schema_base_query);
|
||||
|
||||
if ($schema_base_results) {
|
||||
|
||||
$schema_base_dn = $schema_base_results[0]['subschemasubentry'][0];
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - found that the 'subschemaSubentry' base DN is '$schema_base_dn'",0); }
|
||||
|
||||
$objclass_query = @ ldap_read($ldap_connection,$schema_base_dn,"(objectClasses=*)",array('objectClasses'));
|
||||
if (!$objclass_query) {
|
||||
error_log("$log_prefix LDAP RFC2307BIS detection - unable to query LDAP for objectClasses under ${schema_base_dn}:" . ldap_error($ldap_connection));
|
||||
}
|
||||
else {
|
||||
$objclass_results = @ ldap_get_entries($ldap_connection, $objclass_query);
|
||||
$this_count = $objclass_results[0]['objectclasses']['count'];
|
||||
if ($this_count > 0) {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - found $this_count objectClasses under $schema_base_dn" ,0); }
|
||||
$posixgroup_search = preg_grep("/NAME 'posixGroup'.*AUXILIARY/",$objclass_results[0]['objectclasses']);
|
||||
if (count($posixgroup_search) > 0) {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - found AUXILIARY in posixGroup definition which suggests we're using the RFC2307BIS schema" ,0); }
|
||||
$bis_available = TRUE;
|
||||
}
|
||||
else {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - couldn't find AUXILIARY in the posixGroup definition which suggests we're not using the RFC2307BIS schema. Set FORCE_RFC2307BIS to TRUE if you DO use RFC2307BIS. " ,0); }
|
||||
}
|
||||
}
|
||||
else {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - no objectClasses were returned when searching under $schema_base_dn" ,0); }
|
||||
}
|
||||
}
|
||||
}
|
||||
else {
|
||||
if ($LDAP_DEBUG == TRUE) { error_log("$log_prefix LDAP RFC2307BIS detection - unable to detect the subschemaSubentry base DN" ,0); }
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
$LDAP['rfc2307bis_check_run'] == TRUE;
|
||||
if ($bis_available == TRUE) {
|
||||
if (!isset($LDAP['group_membership_attribute'])) { $LDAP['group_membership_attribute'] = 'uniquemember'; }
|
||||
if (!isset($LDAP['group_membership_uses_uid'])) { $LDAP['group_membership_uses_uid'] = FALSE; }
|
||||
return TRUE;
|
||||
}
|
||||
else {
|
||||
if (!isset($LDAP['group_membership_attribute'])) { $LDAP['group_membership_attribute'] = 'memberuid'; }
|
||||
if (!isset($LDAP['group_membership_uses_uid'])) { $LDAP['group_membership_uses_uid'] = TRUE; }
|
||||
return FALSE;
|
||||
}
|
||||
|
||||
|
||||
}
|
||||
|
||||
?>
|
||||
|
||||
@ -35,7 +35,7 @@ function send_email($recipient_email,$recipient_name,$subject,$body) {
|
||||
return FALSE;
|
||||
}
|
||||
else {
|
||||
error_log("$log_prefix New user: sent a new account email to $recipient_email ($recipient_name)");
|
||||
error_log("$log_prefix SMTP: sent an email to $recipient_email ($recipient_name)");
|
||||
return TRUE;
|
||||
}
|
||||
|
||||
|
||||
@ -3,7 +3,7 @@
|
||||
#Modules and how they can be accessed.
|
||||
|
||||
#access:
|
||||
#user = need to be logged-in to see it
|
||||
#auth = need to be logged-in to see it
|
||||
#hidden_on_login = only visible when not logged in
|
||||
#admin = need to be logged in as an admin to see it
|
||||
|
||||
@ -14,4 +14,8 @@
|
||||
'log_out' => 'auth'
|
||||
);
|
||||
|
||||
if ($ACCOUNT_REQUESTS_ENABLED == TRUE) {
|
||||
$MODULES['request_account'] = 'hidden_on_login';
|
||||
}
|
||||
|
||||
?>
|
||||
|
||||
@ -9,6 +9,7 @@ $ACCESS_LEVEL_NAME = array('account','admin');
|
||||
unset($USER_ID);
|
||||
$CURRENT_PAGE=htmlentities($_SERVER['PHP_SELF']);
|
||||
$SENT_HEADERS = FALSE;
|
||||
$SESSION_TIMED_OUT = FALSE;
|
||||
|
||||
$paths=explode('/',getcwd());
|
||||
$THIS_MODULE_PATH=end($paths);
|
||||
@ -17,6 +18,8 @@ $GOOD_ICON = "☑";
|
||||
$WARN_ICON = "⚠";
|
||||
$FAIL_ICON = "⛔";
|
||||
|
||||
$JS_EMAIL_REGEX='/^(([^<>()[\]\\.,;:\s@\"]+(\.[^<>()[\]\\.,;:\s@\"]+)*)|(\".+\"))@((\[[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\.[0-9]{1,3}\])|(([a-zA-Z\-0-9]+\.)+[a-zA-Z]{2,}))$/;';
|
||||
|
||||
if (isset($_SERVER['HTTPS']) and
|
||||
($_SERVER['HTTPS'] == 'on' || $_SERVER['HTTPS'] == 1) or
|
||||
isset($_SERVER['HTTP_X_FORWARDED_PROTO']) and
|
||||
@ -27,8 +30,8 @@ else {
|
||||
$SITE_PROTOCOL = 'http://';
|
||||
}
|
||||
|
||||
include ("modules.inc.php"); # module definitions
|
||||
include ("config.inc.php"); # get local settings
|
||||
include ("modules.inc.php"); # module definitions
|
||||
|
||||
validate_passkey_cookie();
|
||||
|
||||
@ -50,7 +53,7 @@ function set_passkey_cookie($user_id,$is_admin) {
|
||||
|
||||
# Create a random value, store it locally and set it in a cookie.
|
||||
|
||||
global $LOGIN_TIMEOUT_MINS, $VALIDATED, $USER_ID, $IS_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
global $SESSION_TIMEOUT, $VALIDATED, $USER_ID, $IS_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
|
||||
|
||||
$passkey = generate_passkey();
|
||||
@ -63,7 +66,8 @@ function set_passkey_cookie($user_id,$is_admin) {
|
||||
}
|
||||
$filename = preg_replace('/[^a-zA-Z0-9]/','_', $user_id);
|
||||
@ file_put_contents("/tmp/$filename","$passkey:$admin_val:$this_time");
|
||||
setcookie('orf_cookie', "$user_id:$passkey", $this_time+(60 * $LOGIN_TIMEOUT_MINS), '/', '', '', TRUE);
|
||||
setcookie('orf_cookie', "$user_id:$passkey", $this_time+(60 * $SESSION_TIMEOUT), '/', '', '', TRUE);
|
||||
setcookie('sessto_cookie', $this_time+(60 * $SESSION_TIMEOUT), $this_time+7200, '/', '', '', TRUE);
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: user $user_id validated (IS_ADMIN=${IS_ADMIN}), sent orf_cookie to the browser.",0); }
|
||||
$VALIDATED = TRUE;
|
||||
|
||||
@ -74,7 +78,9 @@ function set_passkey_cookie($user_id,$is_admin) {
|
||||
|
||||
function validate_passkey_cookie() {
|
||||
|
||||
global $LOGIN_TIMEOUT_MINS, $IS_ADMIN, $USER_ID, $VALIDATED, $log_prefix, $SESSION_DEBUG;
|
||||
global $SESSION_TIMEOUT, $IS_ADMIN, $USER_ID, $VALIDATED, $log_prefix, $SESSION_TIMED_OUT, $SESSION_DEBUG;
|
||||
|
||||
$this_time=time();
|
||||
|
||||
if (isset($_COOKIE['orf_cookie'])) {
|
||||
|
||||
@ -89,17 +95,16 @@ function validate_passkey_cookie() {
|
||||
}
|
||||
else {
|
||||
list($f_passkey,$f_is_admin,$f_time) = explode(":",$session_file);
|
||||
$this_time=time();
|
||||
if (!empty($c_passkey) and $f_passkey == $c_passkey and $this_time < $f_time+(60 * $LOGIN_TIMEOUT_MINS)) {
|
||||
if (!empty($c_passkey) and $f_passkey == $c_passkey and $this_time < $f_time+(60 * $SESSION_TIMEOUT)) {
|
||||
if ($f_is_admin == 1) { $IS_ADMIN = TRUE; }
|
||||
$VALIDATED = TRUE;
|
||||
$USER_ID=$user_id;
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Setup session: Cookie and session file values match for user ${user_id} - VALIDATED (ADMIN = ${IS_ADMIN})",0); }
|
||||
set_passkey_cookie($USER_ID,$IS_ADMIN);
|
||||
}
|
||||
elseif ( $SESSION_DEBUG == TRUE ) {
|
||||
else {
|
||||
if ( $SESSION_DEBUG == TRUE ) {
|
||||
$this_error="$log_prefix Session: orf_cookie was sent by the client and the session file was found at /tmp/$filename, but";
|
||||
if ($this_time < $f_time+(60 * $LOGIN_TIMEOUT_MINS)) { $this_error .= " the timestamp was older than the login timeout ($LOGIN_TIMEOUT_MINS);"; }
|
||||
if (empty($c_passkey)) { $this_error .= " the cookie passkey wasn't set;"; }
|
||||
if ($c_passkey != $f_passkey) { $this_error .= " the session file passkey didn't match the cookie passkey;"; }
|
||||
$this_error += " Cookie: ${_COOKIE['orf_cookie']} - Session file contents: $session_file";
|
||||
@ -107,8 +112,17 @@ function validate_passkey_cookie() {
|
||||
}
|
||||
}
|
||||
}
|
||||
elseif ( $SESSION_DEBUG == TRUE) {
|
||||
error_log("$log_prefix Session: orf_cookie wasn't sent by the client.",0);
|
||||
|
||||
}
|
||||
else {
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: orf_cookie wasn't sent by the client.",0); }
|
||||
if (isset($_COOKIE['sessto_cookie'])) {
|
||||
$this_session_timeout = $_COOKIE['sessto_cookie'];
|
||||
if ($this_time >= $this_session_timeout) {
|
||||
$SESSION_TIMED_OUT = TRUE;
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: The session had timed-out (over $SESSION_TIMEOUT mins idle).",0); }
|
||||
}
|
||||
}
|
||||
}
|
||||
|
||||
}
|
||||
@ -120,7 +134,7 @@ function set_setup_cookie() {
|
||||
|
||||
# Create a random value, store it locally and set it in a cookie.
|
||||
|
||||
global $LOGIN_TIMEOUT_MINS, $IS_SETUP_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
global $SESSION_TIMEOUT, $IS_SETUP_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
|
||||
$passkey = generate_passkey();
|
||||
$this_time=time();
|
||||
@ -128,8 +142,8 @@ function set_setup_cookie() {
|
||||
$IS_SETUP_ADMIN = TRUE;
|
||||
|
||||
file_put_contents("/tmp/ldap_setup","$passkey:$this_time");
|
||||
# setcookie('setup_cookie', "$passkey", $this_time+(60 * $LOGIN_TIMEOUT_MINS), '/', $_SERVER["HTTP_HOST"]);
|
||||
setcookie('setup_cookie', "$passkey", $this_time+(60 * $LOGIN_TIMEOUT_MINS), '/', '', '', TRUE);
|
||||
# setcookie('setup_cookie', "$passkey", $this_time+(60 * $SESSION_TIMEOUT), '/', $_SERVER["HTTP_HOST"]);
|
||||
setcookie('setup_cookie', "$passkey", $this_time+(60 * $SESSION_TIMEOUT), '/', '', '', TRUE);
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Setup session: sent setup_cookie to the client.",0); }
|
||||
|
||||
}
|
||||
@ -139,7 +153,7 @@ function set_setup_cookie() {
|
||||
|
||||
function validate_setup_cookie() {
|
||||
|
||||
global $LOGIN_TIMEOUT_MINS, $IS_SETUP_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
global $SESSION_TIMEOUT, $IS_SETUP_ADMIN, $log_prefix, $SESSION_DEBUG;
|
||||
|
||||
if (isset($_COOKIE['setup_cookie'])) {
|
||||
|
||||
@ -151,14 +165,13 @@ function validate_setup_cookie() {
|
||||
}
|
||||
list($f_passkey,$f_time) = explode(":",$session_file);
|
||||
$this_time=time();
|
||||
if (!empty($c_passkey) and $f_passkey == $c_passkey and $this_time < $f_time+(60 * $LOGIN_TIMEOUT_MINS)) {
|
||||
if (!empty($c_passkey) and $f_passkey == $c_passkey and $this_time < $f_time+(60 * $SESSION_TIMEOUT)) {
|
||||
$IS_SETUP_ADMIN = TRUE;
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Setup session: Cookie and session file values match - VALIDATED ",0); }
|
||||
set_setup_cookie();
|
||||
}
|
||||
elseif ( $SESSION_DEBUG == TRUE) {
|
||||
$this_error="$log_prefix Setup session: setup_cookie was sent by the client and the session file was found at /tmp/ldap_setup, but";
|
||||
if ($this_time < $f_time+(60 * $LOGIN_TIMEOUT_MINS)) { $this_error .= " the timestamp was older than the login timeout ($LOGIN_TIMEOUT_MINS);"; }
|
||||
if (empty($c_passkey)) { $this_error .= " the cookie passkey wasn't set;"; }
|
||||
if ($c_passkey != $f_passkey) { $this_error .= " the session file passkey didn't match the cookie passkey;"; }
|
||||
$this_error += " Cookie: ${_COOKIE['setup_cookie']} - Session file contents: $session_file";
|
||||
@ -181,6 +194,7 @@ function log_out($method='normal') {
|
||||
global $USER_ID;
|
||||
|
||||
setcookie('orf_cookie', "", time()-20000, '/', '', '', TRUE);
|
||||
setcookie('sessto_cookie', "", time()-20000, '/', '', '', TRUE);
|
||||
|
||||
$filename = preg_replace('/[^a-zA-Z0-9]/','_', $USER_ID);
|
||||
@ unlink("/tmp/$filename");
|
||||
@ -289,7 +303,7 @@ function render_footer() {
|
||||
|
||||
function set_page_access($level) {
|
||||
|
||||
global $IS_ADMIN, $IS_SETUP_ADMIN, $VALIDATED, $log_prefix, $SESSION_DEBUG;
|
||||
global $IS_ADMIN, $IS_SETUP_ADMIN, $VALIDATED, $log_prefix, $SESSION_DEBUG, $SESSION_TIMED_OUT;
|
||||
|
||||
#Set the security level needed to view a page.
|
||||
#This should be one of the first pieces of code
|
||||
@ -307,13 +321,15 @@ function set_page_access($level) {
|
||||
}
|
||||
}
|
||||
|
||||
if ($SESSION_TIMED_OUT == TRUE) { $reason = "session_timeout"; } else { $reason = "unauthorised"; }
|
||||
|
||||
if ($level == "admin") {
|
||||
if ($IS_ADMIN == TRUE and $VALIDATED == TRUE) {
|
||||
return;
|
||||
}
|
||||
else {
|
||||
header("Location: //" . $_SERVER["HTTP_HOST"] . "/index.php?unauthorised\n\n");
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: UNAUTHORISED: page security level is 'admin' but IS_ADMIN = '${IS_ADMIN}' and VALIDATED = '${VALIDATED}' (user) ",0); }
|
||||
header("Location: //" . $_SERVER["HTTP_HOST"] . "/log_in/index.php?$reason&redirect_to=" . base64_encode($_SERVER['REQUEST_URI']) . "\n\n");
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: no access to page ($reason): page security level is 'admin' but IS_ADMIN = '${IS_ADMIN}' and VALIDATED = '${VALIDATED}' (user) ",0); }
|
||||
exit(0);
|
||||
}
|
||||
}
|
||||
@ -323,8 +339,8 @@ function set_page_access($level) {
|
||||
return;
|
||||
}
|
||||
else {
|
||||
header("Location: //" . $_SERVER["HTTP_HOST"] . "/index.php?unauthorised\n\n");
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: UNAUTHORISED: page security level is 'user' but VALIDATED = '${VALIDATED}'",0); }
|
||||
header("Location: //" . $_SERVER["HTTP_HOST"] . "/log_in/index.php?$reason&redirect_to=" . base64_encode($_SERVER['REQUEST_URI']) . "\n\n");
|
||||
if ( $SESSION_DEBUG == TRUE) { error_log("$log_prefix Session: no access to page ($reason): page security level is 'user' but VALIDATED = '${VALIDATED}'",0); }
|
||||
exit(0);
|
||||
}
|
||||
}
|
||||
@ -369,6 +385,21 @@ EoCheckJS;
|
||||
|
||||
}
|
||||
|
||||
######################################################
|
||||
|
||||
function generate_username($fn,$ln) {
|
||||
|
||||
global $USERNAME_FORMAT;
|
||||
|
||||
$username = $USERNAME_FORMAT;
|
||||
$username = str_replace('{first_name}',strtolower($fn), $username);
|
||||
$username = str_replace('{first_name_initial}',strtolower($fn[0]), $username);
|
||||
$username = str_replace('{last_name}',strtolower($ln), $username);
|
||||
$username = str_replace('{first_name_initial}',strtolower($ln[0]), $username);
|
||||
|
||||
return $username;
|
||||
|
||||
}
|
||||
|
||||
######################################################
|
||||
|
||||
@ -377,7 +408,7 @@ function render_js_username_generator($firstname_field_id,$lastname_field_id,$us
|
||||
#Parameters are the IDs of the input fields and username name div in the account creation form.
|
||||
#The div will be set to warning if the username is invalid.
|
||||
|
||||
global $USERNAME_FORMAT, $USERNAME_REGEX;
|
||||
global $USERNAME_FORMAT;
|
||||
|
||||
render_js_username_check();
|
||||
|
||||
|
||||
@ -5,15 +5,6 @@ include_once "web_functions.inc.php";
|
||||
|
||||
render_header();
|
||||
|
||||
if (isset($_GET['logged_out'])) {
|
||||
?>
|
||||
<div class="alert alert-warning">
|
||||
<p class="text-center">You've been automatically logged out because you've been inactive for over
|
||||
<?php print $LOGIN_TIMEOUT_MINS; ?> minutes. Click on the 'Log in' link to get back into the system.</p>
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
|
||||
if (isset($_GET['logged_in'])) {
|
||||
?>
|
||||
<div class="alert alert-success">
|
||||
@ -22,13 +13,5 @@ render_header();
|
||||
<?php
|
||||
}
|
||||
|
||||
if (isset($_GET['unauthorised'])) {
|
||||
?>
|
||||
<div class="alert alert-danger">
|
||||
<p class="text-center">You don't have the necessary permissions needed to use this module.</p>
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
|
||||
render_footer();
|
||||
?>
|
||||
|
||||
@ -5,6 +5,20 @@ set_include_path( ".:" . __DIR__ . "/../includes/");
|
||||
include "web_functions.inc.php";
|
||||
include "ldap_functions.inc.php";
|
||||
|
||||
if (isset($_GET["unauthorised"])) { $display_unauth = TRUE; }
|
||||
if (isset($_GET["session_timeout"])) { $display_logged_out = TRUE; }
|
||||
if (isset($_GET["redirect_to"])) { $redirect_to = $_GET["redirect_to"]; }
|
||||
|
||||
if (isset($_GET['logged_out'])) {
|
||||
?>
|
||||
<div class="alert alert-warning">
|
||||
<p class="text-center">You've been automatically logged out because you've been inactive for over
|
||||
<?php print $SESSION_TIMEOUT; ?> minutes. Click on the 'Log in' link to get back into the system.</p>
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
|
||||
|
||||
if (isset($_POST["user_id"]) and isset($_POST["password"])) {
|
||||
|
||||
$ldap_connection = open_ldap_connection();
|
||||
@ -16,15 +30,15 @@ if (isset($_POST["user_id"]) and isset($_POST["password"])) {
|
||||
if ($user_auth != FALSE) {
|
||||
|
||||
set_passkey_cookie($user_auth,$is_admin);
|
||||
if (isset($_POST["sendto"])) {
|
||||
header("Location: //${_SERVER["HTTP_HOST"]}${_POST["sendto"]}\n\n");
|
||||
if (isset($_POST["redirect_to"])) {
|
||||
header("Location: //${_SERVER['HTTP_HOST']}" . base64_decode($_POST['redirect_to']) . "\n\n");
|
||||
}
|
||||
else {
|
||||
header("Location: //${_SERVER["HTTP_HOST"]}/index.php?logged_in\n\n");
|
||||
header("Location: //${_SERVER['HTTP_HOST']}/index.php?logged_in\n\n");
|
||||
}
|
||||
}
|
||||
else {
|
||||
header("Location: //${_SERVER["HTTP_HOST"]}/${THIS_MODULE_PATH}/index.php?invalid\n\n");
|
||||
header("Location: //${_SERVER['HTTP_HOST']}/${THIS_MODULE_PATH}/index.php?invalid\n\n");
|
||||
}
|
||||
|
||||
}
|
||||
@ -40,15 +54,26 @@ else {
|
||||
<div class="panel-heading text-center">Log in</div>
|
||||
<div class="panel-body text-center">
|
||||
|
||||
<?php if (isset($display_unauth)) { ?>
|
||||
<div class="alert alert-warning">
|
||||
Please log in to continue
|
||||
</div>
|
||||
<?php } ?>
|
||||
|
||||
<?php if (isset($display_logged_out)) { ?>
|
||||
<div class="alert alert-warning">
|
||||
You were logged out because your session expired. Log in again to continue.
|
||||
</div>
|
||||
<?php } ?>
|
||||
|
||||
<?php if (isset($_GET["invalid"])) { ?>
|
||||
<div class="alert alert-warning">
|
||||
The username and/or password are unrecognised.
|
||||
</div>
|
||||
<?php } ?>
|
||||
|
||||
|
||||
<form class="form-horizontal" action='' method='post'>
|
||||
<?php if (isset($sendto) and ($sendto != "")) { ?><input type="hidden" name="sendto" value="<?php print $sendto; ?>"><?php } ?>
|
||||
<?php if (isset($redirect_to) and ($redirect_to != "")) { ?><input type="hidden" name="redirect_to" value="<?php print $redirect_to; ?>"><?php } ?>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="username" class="col-sm-4 control-label">Username</label>
|
||||
@ -57,7 +82,6 @@ else {
|
||||
</div>
|
||||
</div>
|
||||
|
||||
|
||||
<div class="form-group">
|
||||
<label for="password" class="col-sm-4 control-label">Password</label>
|
||||
<div class="col-sm-6">
|
||||
|
||||
BIN
www/request_account/fonts/font_01.ttf
Normal file
BIN
www/request_account/fonts/font_01.ttf
Normal file
Binary file not shown.
BIN
www/request_account/fonts/font_02.ttf
Normal file
BIN
www/request_account/fonts/font_02.ttf
Normal file
Binary file not shown.
BIN
www/request_account/fonts/font_03.ttf
Normal file
BIN
www/request_account/fonts/font_03.ttf
Normal file
Binary file not shown.
BIN
www/request_account/fonts/font_04.ttf
Normal file
BIN
www/request_account/fonts/font_04.ttf
Normal file
Binary file not shown.
76
www/request_account/human.php
Normal file
76
www/request_account/human.php
Normal file
@ -0,0 +1,76 @@
|
||||
<?php
|
||||
|
||||
session_start();
|
||||
|
||||
$image_width=180;
|
||||
$image_height=60;
|
||||
|
||||
##
|
||||
|
||||
function random_string($length = 6) {
|
||||
|
||||
$charset = str_split('ABCDEFGHKLMNPQRSTVWXYZ@$3456789');
|
||||
$randomstr = "";
|
||||
for($i = 0; $i < $length; $i++) {
|
||||
$randomstr .= $charset[array_rand($charset, 1)];
|
||||
}
|
||||
return $randomstr;
|
||||
|
||||
}
|
||||
|
||||
##
|
||||
|
||||
$image = imagecreatetruecolor($image_width, $image_height);
|
||||
imageantialias($image, true);
|
||||
|
||||
$cols = [];
|
||||
|
||||
$r = rand(100, 200);
|
||||
$g = rand(100, 200);
|
||||
$b = rand(100, 200);
|
||||
|
||||
for($i = 0; $i < 5; $i++) {
|
||||
$cols[] = imagecolorallocate($image, $r - 20*$i, $g - 20*$i, $b - 20*$i);
|
||||
}
|
||||
|
||||
imagefill($image, 0, 0, $cols[0]);
|
||||
|
||||
$thickness = rand(2, 10);
|
||||
|
||||
for($i = 0; $i < 10; $i++) {
|
||||
imagesetthickness($image, $thickness);
|
||||
$line_col = $cols[rand(1,4)];
|
||||
imagerectangle($image, rand(-$thickness, ($image_width - $thickness)),
|
||||
rand(-$thickness, $thickness),
|
||||
rand(-$thickness, ($image_width - $thickness)),
|
||||
rand(($image_height - $thickness), ($image_width / 2)),
|
||||
$line_col);
|
||||
}
|
||||
|
||||
$black = imagecolorallocate($image, 0, 0, 0);
|
||||
$white = imagecolorallocate($image, 255, 255, 255);
|
||||
$textcols = [$black, $white];
|
||||
|
||||
$fonts = glob(dirname(__FILE__).'/fonts/*.ttf');
|
||||
$num_chars = 6;
|
||||
$human_proof = random_string($num_chars);
|
||||
|
||||
$_SESSION['proof_of_humanity'] = $human_proof;
|
||||
|
||||
for($i = 0; $i < $num_chars; $i++) {
|
||||
$gap = ($image_width-15)/$num_chars;
|
||||
$size = rand(20,30);
|
||||
$angle = rand(-30,30);
|
||||
$txt_x = 10 + ($i * $gap);
|
||||
$txt_y = rand(30, ($image_height-15));
|
||||
$txt_col = $textcols[rand(0,1)];
|
||||
$txt_font = $fonts[array_rand($fonts)];
|
||||
$txt = $human_proof[$i];
|
||||
imagettftext($image, $size, $angle, $txt_x, $txt_y, $txt_col, $txt_font, $txt);
|
||||
# print "imagettftext( $size, $angle, $txt_x, $txt_y, $txt_col, $txt_font, $txt);<p>";
|
||||
}
|
||||
|
||||
header('Content-type: image/png');
|
||||
imagepng($image);
|
||||
imagedestroy($image);
|
||||
?>
|
||||
176
www/request_account/index.php
Normal file
176
www/request_account/index.php
Normal file
@ -0,0 +1,176 @@
|
||||
<?php
|
||||
|
||||
set_include_path( ".:" . __DIR__ . "/../includes/");
|
||||
session_start();
|
||||
|
||||
include "web_functions.inc.php";
|
||||
|
||||
render_header("Request an account");
|
||||
|
||||
if ($ACCOUNT_REQUESTS_ENABLED == FALSE) {
|
||||
|
||||
?><div class='alert alert-warning'><p class='text-center'>Account requesting is disabled.</p></div><?php
|
||||
|
||||
render_footer();
|
||||
exit(0);
|
||||
|
||||
}
|
||||
|
||||
if($_POST) {
|
||||
|
||||
$error_messages = array();
|
||||
|
||||
if(! isset($_POST['validate']) or strcasecmp($_POST['validate'], $_SESSION['proof_of_humanity']) != 0) {
|
||||
array_push($error_messages, "The validation text didn't match the image.");
|
||||
}
|
||||
|
||||
if (! isset($_POST['firstname']) or $_POST['firstname'] == "") {
|
||||
array_push($error_messages, "You didn't enter your first name.");
|
||||
}
|
||||
else {
|
||||
$firstname=filter_var($_POST['firstname'], FILTER_SANITIZE_STRING);
|
||||
}
|
||||
|
||||
if (! isset($_POST['lastname']) or $_POST['lastname'] == "") {
|
||||
array_push($error_messages, "You didn't enter your first name.");
|
||||
}
|
||||
else {
|
||||
$lastname=filter_var($_POST['lastname'], FILTER_SANITIZE_STRING);
|
||||
}
|
||||
|
||||
if (isset($_POST['email']) and $_POST['email'] != "") {
|
||||
$email=filter_var($_POST['email'], FILTER_SANITIZE_EMAIL);
|
||||
}
|
||||
|
||||
if (isset($_POST['notes']) and $_POST['notes'] != "") {
|
||||
$notes=filter_var($_POST['notes'], FILTER_SANITIZE_STRING);
|
||||
}
|
||||
|
||||
|
||||
if (count($error_messages) > 0) { ?>
|
||||
<div class="alert alert-danger" role="alert">
|
||||
The request couldn't be sent because:
|
||||
<p>
|
||||
<ul>
|
||||
<?php
|
||||
foreach($error_messages as $message) {
|
||||
print "<li>$message</li>\n";
|
||||
}
|
||||
?>
|
||||
</ul>
|
||||
</div>
|
||||
<?php
|
||||
}
|
||||
else {
|
||||
|
||||
$mail_subject = "$firstname $lastname has requested an account for $ORGANISATION_NAME.";
|
||||
|
||||
$link_url="${SITE_PROTOCOL}${SERVER_HOSTNAME}/account_manager/new_user.php?account_request&first_name=$firstname&last_name=$lastname&email=$email";
|
||||
|
||||
if (!isset($email)) { $email = "n/a"; }
|
||||
if (!isset($notes)) { $notes = "n/a"; }
|
||||
|
||||
$mail_body = <<<EoT
|
||||
A request for an $ORGANISATION_NAME account has been sent:
|
||||
|
||||
First name: $firstname
|
||||
Last name: $lastname
|
||||
Email: $email
|
||||
Notes: $notes
|
||||
|
||||
You can create the account at $link_url
|
||||
|
||||
EoT;
|
||||
|
||||
include_once "mail_functions.inc.php";
|
||||
$sent_email = send_email($ACCOUNT_REQUESTS_EMAIL,"$ORGANISATION_NAME account requests",$mail_subject,$mail_body);
|
||||
if ($sent_email) {
|
||||
$sent_email_message .= " Thank you. The request was sent and the administrator will process it as soon as possible.";
|
||||
}
|
||||
else {
|
||||
$sent_email_message .= " Unfortunately the request wasn't sent because of a technical problem.";
|
||||
}
|
||||
?>
|
||||
<div class="container">
|
||||
<div class="col-sm-8">
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-body"><?php print $sent_email_message; ?></div>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
<?php
|
||||
|
||||
render_footer();
|
||||
exit(0);
|
||||
|
||||
}
|
||||
}
|
||||
?>
|
||||
<div class="container">
|
||||
<div class="col-sm-8">
|
||||
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-body">
|
||||
Use this form to send a request for an account to an administrator at <?php print $ORGANISATION_NAME; ?>.
|
||||
If the administrator approves your request they'll get in touch with you to give you your new credentials.
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-heading text-center">Request an account for <?php print $ORGANISATION_NAME; ?></div>
|
||||
<div class="panel-body text-center">
|
||||
|
||||
<form class="form-horizontal" action='' method='post'>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="firstname" class="col-sm-4 control-label">First name</label>
|
||||
<div class="col-sm-6">
|
||||
<input type="text" class="form-control" id="firstname" name="firstname" placeholder="Required" <?php if (isset($firstname)) { print "value='$firstname'"; } ?>>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="lastname" class="col-sm-4 control-label">Last name</label>
|
||||
<div class="col-sm-6">
|
||||
<input type="text" class="form-control" id="lastname" name="lastname" placeholder="Required" <?php if (isset($lastname)) { print "value='$lastname'"; } ?>>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="email" class="col-sm-4 control-label">Email</label>
|
||||
<div class="col-sm-6">
|
||||
<input type="text" class="form-control" id="email" name="email" <?php if (isset($email)) { print "value='$email'"; } ?>>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="Notes" class="col-sm-4 control-label">Notes</label>
|
||||
<div class="col-sm-6">
|
||||
<textarea class="form-control" id="notes" name="notes" placeholder="Enter any extra information you think the administrator might need to know."><?php if (isset($notes)) { print $notes; } ?></textarea>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
<label for="validate" class="col-sm-4 control-label">Validation</label>
|
||||
<div class="col-sm-6">
|
||||
<span class="center-block">
|
||||
<img src="human.php" class="human-check" alt="Non-human detection">
|
||||
<button type="button" class="btn btn-default btn-sm" onclick="document.querySelector('.human-check').src = 'human.php?' + Date.now()">
|
||||
<span class="glyphicon glyphicon-refresh"></span> Refresh
|
||||
</button>
|
||||
</span>
|
||||
<input type="text" class="form-control center-block" id="validate" name="validate" placeholder="Enter the characters from the image">
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="form-group">
|
||||
<button type="submit" class="btn btn-default">Send request</button>
|
||||
</div>
|
||||
|
||||
</form>
|
||||
</div>
|
||||
</div>
|
||||
</div>
|
||||
<?php
|
||||
render_footer();
|
||||
?>
|
||||
@ -49,6 +49,44 @@ else {
|
||||
}
|
||||
|
||||
|
||||
?>
|
||||
</ul>
|
||||
</div>
|
||||
</div>
|
||||
|
||||
<div class="panel panel-default">
|
||||
<div class="panel-heading">LDAP RFC2307BIS schema check</div>
|
||||
<div class="panel-body">
|
||||
<ul class="list-group">
|
||||
<?php
|
||||
|
||||
$bis_detected = ldap_detect_rfc2307bis($ldap_connection);
|
||||
|
||||
if ($bis_detected == TRUE) {
|
||||
|
||||
if ($LDAP['forced_rfc2307bis'] == TRUE) {
|
||||
print "$li_warn FORCE_RFC2307BIS is set to TRUE which means the user manager skipped auto-detecting the RFC2307BIS schema. This could result in errors when creating groups if your LDAP server hasn't actually got the RFC2307BIS schema available. ";
|
||||
}
|
||||
else {
|
||||
print "$li_good The RFC2307BIS schema appears to be available. ";
|
||||
}
|
||||
print "<a href='#' data-toggle='popover' title='RFC2307BIS schema' data-content='";
|
||||
print "The RFC2307BIS schema enhances posixGroups, allowing you to use \"memberOf\" in LDAP searches.";
|
||||
print "'>What's this?</a>";
|
||||
print "</li>\n";
|
||||
|
||||
}
|
||||
else {
|
||||
|
||||
print "$li_warn The RFC2307BIS schema doesn't appear to be available.<br>\nIf this is incorrect, set FORCE_RFC2307BIS to TRUE, restart the user manager and run the setup again. ";
|
||||
print "<a href='#' data-toggle='popover' title='RFC2307BIS' data-content='";
|
||||
print "The RFC2307BIS schema enhances posixGroups, allowing for memberOf LDAP searches.";
|
||||
print "'>What's this?</a>";
|
||||
print "</li>\n";
|
||||
|
||||
}
|
||||
|
||||
|
||||
?>
|
||||
</ul>
|
||||
</div>
|
||||
|
||||
Loading…
x
Reference in New Issue
Block a user